What is a Buffer Overflow Attack Types and Prevention Methods
5 (775) · € 36.00 · Auf Lager
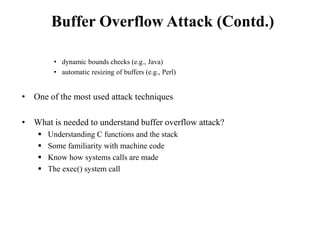
Control hijacking
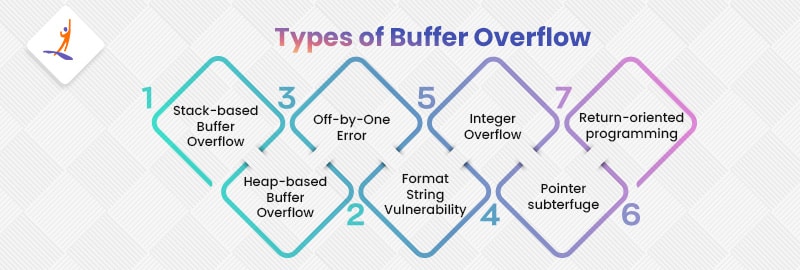
Buffer Overflow in Cyber Security - What is, Types, & Consequences

ROP and Buffer Overflow: A Deadly Duo in Cybersecurity Exploits - FasterCapital

How to Prevent Buffer Overflow Attacks in Software

Defeating buffer overflow attacks via virtualization - ScienceDirect

A buffer overflow detection and defense method based on RISC-V instruction set extension, Cybersecurity

SigFree: A Signature-Free Buffer Overrun and Overflow Attack Blocker
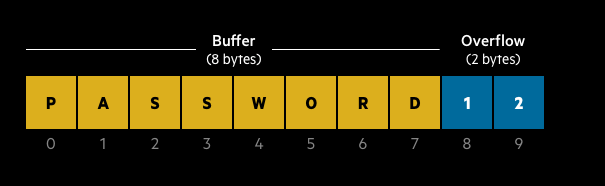
Buffer Overflow Attack. A buffer overflow attack is a cyber…, by Ajay Yadav

Buffer Overflow Attack Types and Prevention Methods

Buffer Overflow Attacks: Detect, Exploit, Prevent: Deckard, Jason: 9781932266672: : Books
Buffer Overflow Protection Tutorial
Buffer Overflow Attacks Explained (with Examples)

Buffer overflow - Wikipedia
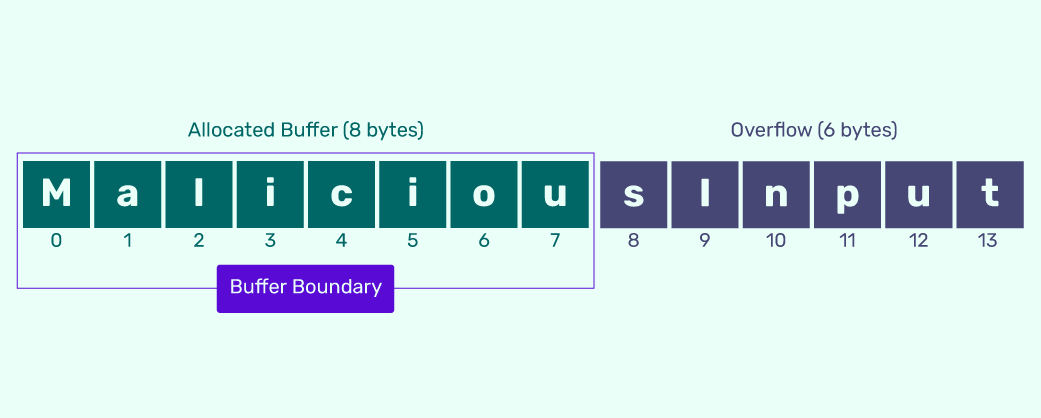
What is a Buffer Overflow Attack?
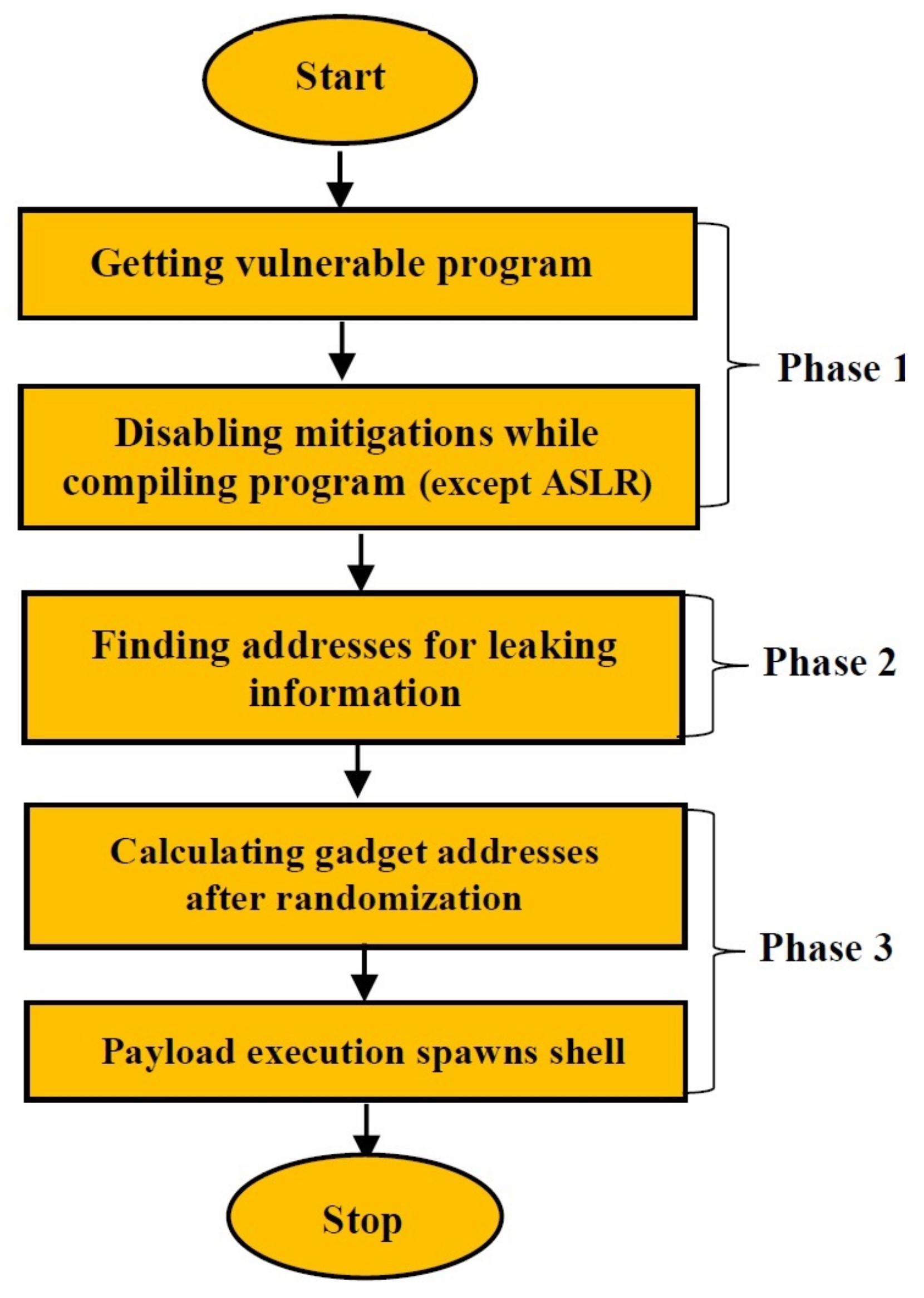
Applied Sciences, Free Full-Text